With hacking strategies and cybersecurity threats evolving on a regular basis, significantly with the quick progress of AI in current months, e mail safety has change into a essential side of security at work and at house.
Hackers can use your e mail each for the content material and as a approach into your group to conduct a breach of the bigger community. As soon as in, hackers can slither their approach into many recordsdata, from confidential monetary information to private data. Right here you can see useful details about the widespread threats to e mail safety and ten greatest practices for a sturdy e mail safety resolution.
Threats to e mail safety
The next are among the commonest threats to e mail safety.
Phishing is an assault that asks you for cash or beneficial data corresponding to account logins or passwords. Spear phishing is an assault that makes use of your private data to get beneficial information by impersonating somebody you understand.
Spoofing is an assault the place false information is offered to look respectable, corresponding to sending an e mail from an account that seems to be an official banking e mail deal with.
Malware is a pc virus, a sort of software program that may get downloaded to your gadget, which is designed to disrupt a tool, server, or community and customarily causes havoc. Malware is a major risk to e mail safety and may be simply downloaded by means of spam when hackers use it to insert malicious hyperlinks, malware, and trojans. Due to this fact, it is essential to take applicable measures to guard your e mail accounts and the contents of your emails from cyber assaults and on-line safety threats.
A DoS assault, or denial-of-service assault, is when a hacker makes a machine or community useful resource unavailable to customers by disrupting the companies of a number linked to a community.
- Growing and evolving cyber assaults
Cyber assaults have gotten more and more refined as AI evolves and helps hackers to write down extra convincing emails. For this reason it’s important to develop a sturdy e mail safety resolution.
12 greatest practices for a robust e mail safety resolution
So, with the entire above in thoughts, let’s delve into some methods to mitigate the dangers posed by cybersecurity with some easy greatest practices which you can apply instantly.
1. Make sturdy passwords and encryptions
Everyone knows that we must always use sturdy passwords and keep away from utilizing the identical one twice, however it may be an actual ache. Generally remembering your cellphone quantity is difficult, not to mention dozens of passwords. Fortunately, many gadgets can safely retailer your passwords so that you just don’t must enter them every time, and a few apps retailer your passwords for you.
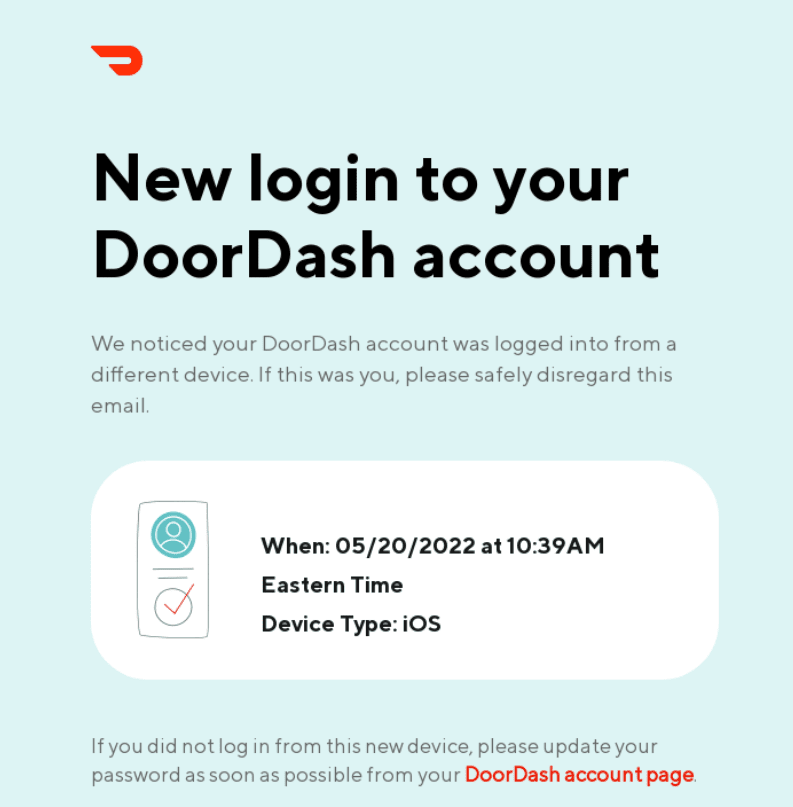
(Supply: Actually Good Emails)
Subsequent, we now have encryption: each time you ship a thank-you e mail (or any e mail for that matter), there’s some danger that it is going to be intercepted by a hacker on its journey between you — the sender — and the recipient. So what does encryption do? It scrambles your e mail’s content material so anybody intercepting it may’t learn it. Solely with authentication from the recipient can the true message be learn. This additionally implies that should you unintentionally ship an e mail to the mistaken deal with, the recipient received’t be capable to learn it.
Many e mail companies, corresponding to Gmail and Microsoft Outlook, in addition to safe e mail suppliers like Mailfence, supply encryption as a characteristic. Defending your inner audit report instance and different important paperwork turns into a lot simpler with encryption.
2. Again up your vital emails
In addition to defending your information from being seen by undesirable eyes, you additionally wish to shield it from getting misplaced or deleted. For this reason it’s an incredible concept at all times to again up any vital emails. You may go for an exterior laborious drive or a USB stick or add information to the cloud.
There are advantages and downsides to all of those. A bodily exterior laborious drive or USB stick can get misplaced or broken, and there have been situations previously of hackers moving into cloud storage options and stealing information that approach.
There is no such thing as a excellent resolution, however safety for cloud storage has improved over time. Having a bodily copy of your vital information can assist in case your gadget decides to exit the land of the residing.
3. Educate everybody about suspicious emails and hyperlinks
Whereas quite a lot of cybersecurity comes right down to tech, a superb quantity of it’s about widespread sense and educating greatest practices, corresponding to learn how to acknowledge and cope with suspicious-looking emails or use e mail monitoring software program. You may run easy webinars, use video tutorials to simplify the method and add a quiz to make sure everybody has reached a particular customary throughout the group.
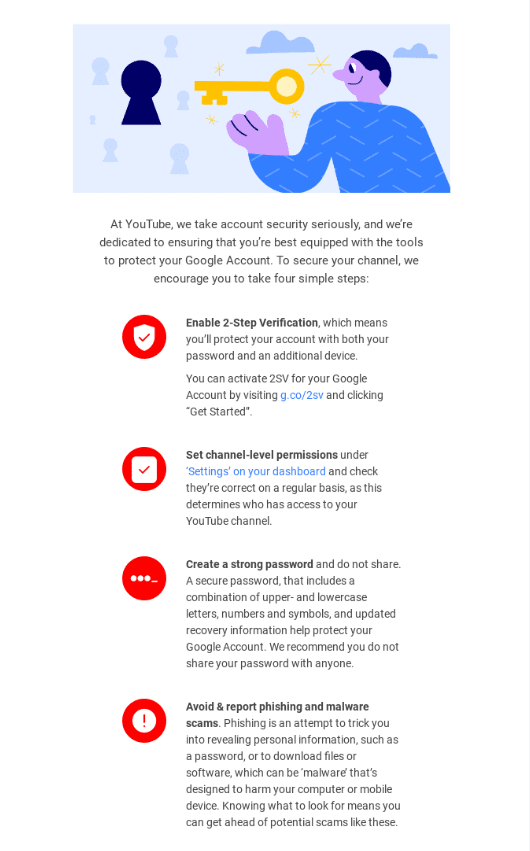
(Supply: E-mail from YouTube)
Annual refreshers with up to date data would additionally assist the method, and you’ll take a look at the SOC 2 certification price if you wish to go the additional mile with coaching your employees in all issues audit-related.
4. Hold your accessibility confidential
Proxies help you hold your location data personal, ship emails and conduct on-line analysis with out worrying about Google third-party cookies monitoring you. Particularly for emails, proxies help you ship them with out exposing your IP deal with.
So how does it work? Proxy servers act as a gateway between you and the web, separating you and different customers from the web sites you browse. Web site visitors goes by means of the proxy server to the deal with you typed in. The request comes again by means of that very same proxy server, and you might be forwarded the information acquired from the web site.
5. Set up up-to-date antivirus safety
You may’t simply ignore your antivirus and depart it within the nook. It wants consideration generally, so don’t ignore these pop-ups telling you that it’s essential to obtain the newest model of the app. An previous model will rapidly change into out of date towards the fixed tide of hacking, so guarantee your defenses are fortified with the newest updates and dependable e mail safety instruments.
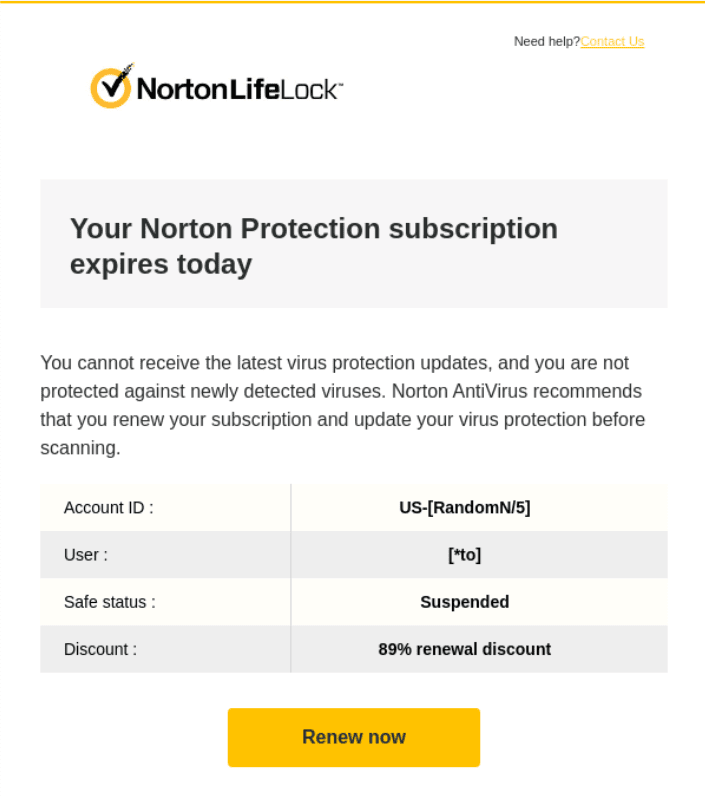
(Supply: Actually Good Emails)
6. Enhance your spam filter
You should utilize an e mail content material filter to intercept incoming messages and examine them for malware or different harmful components. After this course of, your “How safe is RDP?” e mail will get delivered to its vacation spot or quarantined so that you can overview if vital.
Screening incoming communications earlier than they attain you or your group can shield you massively. This course of permits you to have a look at messages with out opening them and block spam messages and malware earlier than they’ll attain your colleagues’ inboxes.
One other efficient approach to enhance e mail safety is to make use of e mail verification instruments. These instruments can assist be certain that solely respectable emails are delivered to your inbox whereas blocking spam and phishing makes an attempt.
With so many choices available on the market, figuring out which instruments are the very best to your wants may be tough. To make the choice course of simpler, it is price trying out among the greatest e mail verification instruments accessible and discovering one which fits your group’s necessities.
7. Make your e mail advertising and marketing contact checklist safe
That is essential for sustaining your prospects and audiences’ belief. In any case, digital safety isn’t solely about your information but in addition your prospects’ information. In relation to e mail, this implies taking good care of your e mail advertising and marketing contact checklist.
To do that, it’s best to be sure you restrict who has entry to your e mail advertising and marketing checklist and retailer it securely in restricted locations (e.g., in a safe database). It is because the extra people who have entry and the extra copies that exist, the extra possible it’s that the checklist will likely be compromised.
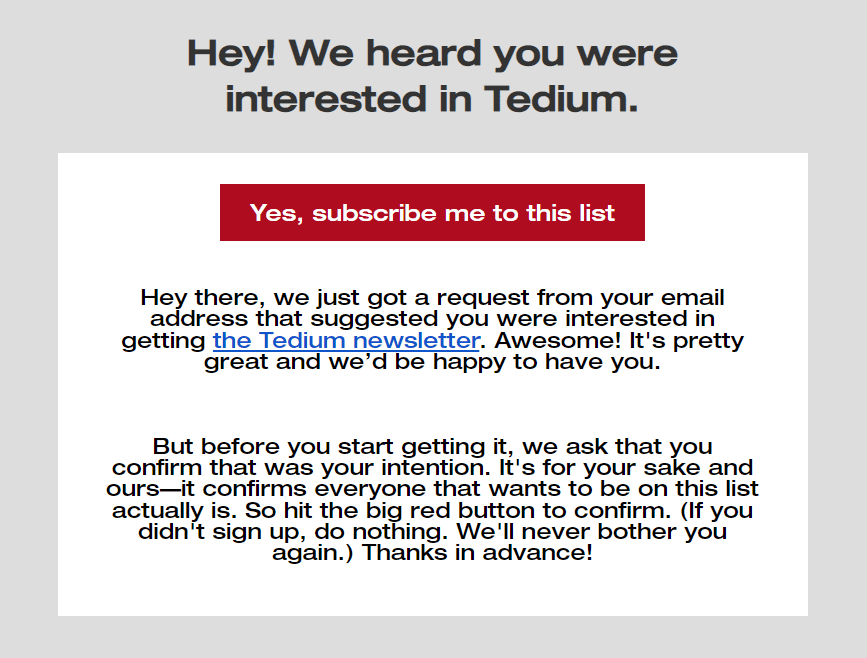
(Supply: E-mail from Tedium)
You possibly can additionally contemplate establishing a double opt-in sign-up course of, which creates a further step for patrons to subscribe to a mailing checklist. It will cut back the chance that your advertising and marketing emails are being despatched to bots or invalid e mail addresses, in addition to guarantee your prospects that they received’t be receiving emails they don’t need.
8. Allow SPF, DKIM, and DMARC authentication
There are three kinds of e mail authentication which you can configure: Sender Coverage Framework (SPF), Domainkeys Recognized Mail (DKIM), and Area-based Message Authentication, Reporting & Conformance (DMARC). Collectively they assist mailbox suppliers and spam filters to acknowledge that your e mail is respectable and may be trusted.
This fulfills two goals. Firstly, they’re important configurations that shield your model’s status. It is because they cut back the chance of an unauthorized consumer sending emails beneath your area with out your consent or data.
On high of this, in addition they be certain that the emails you ship attain their desired recipient. Decreasing the danger that they find yourself in a buyer’s or shopper’s spam folder or are flagged as a risk.
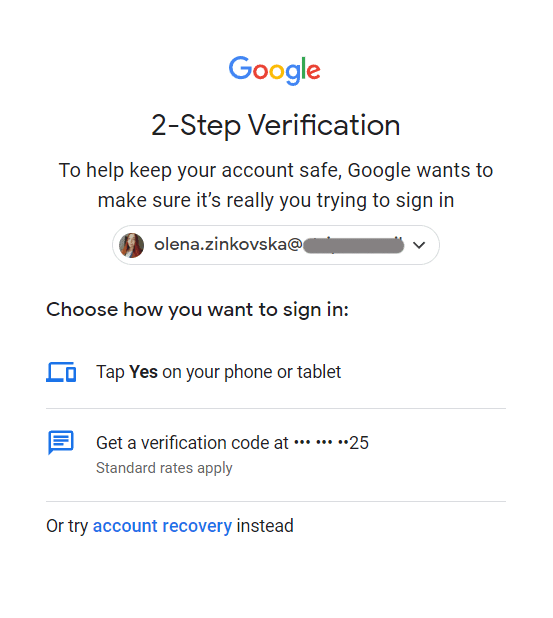
9. Allow two-factor authentication
Two-factor and multifactor authentication are nice choices that massively improve your e mail safety.
That is the way it works: once you log in to your e mail, you enter your password, which triggers a code despatched to your smartphone for verification. With out this code, you possibly can’t entry your account, so even when a hacker had been to get their arms in your password, your data would stay protected.
10. Replace your OS
Frequently updating your working system is significant for e mail safety since updates can add new options. Updates additionally repair or patch any vulnerabilities within the system. Patches take away bugs and gaps that hackers may use to achieve entry to your laptop and information.
11. Solely belief dependable sources
In the event you obtain an e mail with a hyperlink to click on on, at all times examine the place that hyperlink goes to direct you earlier than clicking on it. You may sort the web site deal with into your browser to make sure that it is not going to redirect you to a pretend web site.
If it seems to be suspicious for any cause, do not click on on it, even when it seems to have been despatched from somebody you understand. As a substitute, it’s best to contact the individual and ask in the event that they despatched you the e-mail.
Studying the tell-tell indicators of a phishing e mail may prevent quite a lot of stress and fear and is essential in e mail administration. The next are indicators that an e mail is a rip-off, even when it seems to be prefer it comes from an organization you belief and even makes use of its emblem:
- a generic greeting or the primary half of the e-mail as an alternative of your title. You already know the drill: “Hi there ant_man_fan78..”;
- the e-mail claims that your account is on maintain due to a billing drawback;
- the e-mail asks you to click on on a hyperlink to replace your cost particulars.
Actual firms won’t ever e mail or textual content with a hyperlink to replace your cost data. It’s additionally extraordinarily uncommon for respectable firms to ship emails with typos, which is one other widespread signal of phishing emails. Nevertheless, AI is making it simpler for hackers to enhance the grammar of phishing emails.
12. Implement worker compliance
Lastly, all of this data is ineffective except utilized, so be certain that your colleagues and workers (and employers!) are taking heed of e mail safety protocols and making use of them as vital.
To remain forward of the curve, be sure that to recurrently overview and replace your e mail lists and put money into respected checklist administration instruments. Maintaining with the newest developments in e mail safety can assist shield your online business from potential cyber-attacks. Overview The E-mail Record Decay Report for 2023 for extra insights.
Wrapping up
Preserving your emails protected isn’t rocket science, nevertheless it requires some forethought and consideration, particularly should you’re operating a enterprise of any measurement. Nobody is protected from hacking or trying like a gorgeous goal.
For this reason it’s essential to shield your e mail and information and again the whole lot up. Whether or not you’re an e mail marketer or an accountant at your organization, should you work with emails (and virtually all of us do), it’s essential to know what’s up with safety.
Be part of Stripo to avoid wasting time and construct skilled emails stress-free

